According to Google, DarkSword affects iOS versions 18.4–18.7. It chains six vulnerabilities to achieve remote code execution and deploy a final-stage payload. Researchers identified three malware families associated with successful attacks: GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. Google noted that the reuse of the same exploit chain across multiple actors resembles the previously discovered Coruna exploit kit.

DarkSword exploit chain and capabilities
According to Google, DarkSword combines six vulnerabilities to breach vulnerable devices. Three of them affect WebKit — the engine behind Safari and all browsers on iOS and iPadOS. Two vulnerabilities are located in the iOS and macOS kernel, while one targets Apple’s Dynamic Link Editor.
Lookout researchers describe DarkSword as “a complete exploit chain and infostealer written in JavaScript.” The attack begins when Safari loads a malicious iframe embedded within a webpage. The exploit then escapes the WebContent sandbox and uses WebGPU to inject into the mediaplaybackd process.
At this stage, attackers gain kernel-level read and write access, allowing them to interact with privileged processes and weaken sandbox protections. As a result, the malware can access protected areas of the filesystem. The main script then executes several auxiliary modules that collect passwords, encryption keys, and files, transmitting them to attacker-controlled servers.
Campaigns across regions
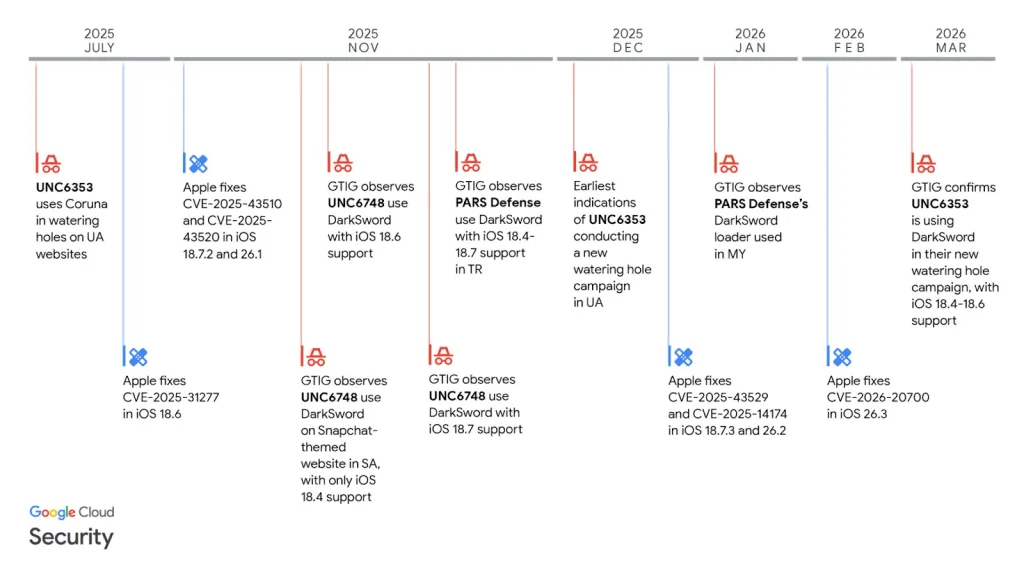
Google reports that the group UNC6748 used DarkSword in November 2025 against users in Saudi Arabia via a Snapchat-themed website. In separate operations in November 2025 and January 2026, campaigns linked to PARS Defense customers targeted users in Turkey and Malaysia.
Google also links DarkSword to the group UNC6353, believed to be associated with Russian intelligence. The group previously used the Coruna exploit and, in this campaign, deployed DarkSword along with the GHOSTBLADE backdoor against users in Ukraine.
Researchers note that GHOSTBLADE collects a wide range of data, including device information, installed applications, accounts, location history, photos, calendar entries, notes, cryptocurrency wallet data, and Safari browsing history. The Ukrainian campaign was also analyzed by iVerify.
Links to Coruna and suspicious infrastructure
Two weeks earlier, Google and iVerify disclosed Coruna — a spyware-grade iOS exploit kit used in commercial surveillance, cyber espionage, and cybercrime. Coruna includes five exploit chains and 23 exploits. Compared to it, DarkSword uses fewer vulnerabilities but achieves similar outcomes.
Following the Coruna disclosure, Lookout researchers identified a suspicious domain cdncounter[.]net linked to infrastructure associated with UNC6748. It was used via compromised Ukrainian websites containing hidden iframes.
Further analysis showed that these attacks did not use Coruna, but instead relied on DarkSword. The malicious code fingerprinted devices and targeted specific iOS versions.
According to researchers, both Coruna and DarkSword can be used not only for cyber espionage but also for cryptocurrency theft. This leaves open the question of attacker motives — financial, intelligence-driven, or a combination of both.


